The Ugliness of War and Technocracy
A look at weapons of war in the digital age.
By Gabriel
Published: Jun 16 2024
Cyberwar
Automation
Cognitive Warfare
Government
War
Surveillance
For those interested in preserving our nations, free markets, culture, or even basic human rights, we are in an outright harrowing time. Many of these challenges are direct physical assaults like warfare, but there is also a wide variety of abstract dangers. Such as censorship, surveillance, economic warfare, or disaster capitalism. Governments battle against their people for control over policy, and against mega-corporations for control over the public. Families, communities, even entire nations are stuck in the crossfire of larger plans without clear allies to depend on. Marshall McLuhan’s quote has become a tired cliche these days as more and more people recognize that vast swaths of humanity are under attack from seemingly every direction.
“World War 3 is a guerrilla information war with no division between military and civilian participation.”
The quote accurately describes what many are feeling, but little else.
It leaves behind many questions to ponder further:
- What is the war about?
- Who’s waging the war, and against whom?
- Who’s winning?
- Is there a side to join or oppose?
- When will it be over?
- What can we do to protect ourselves?
I don’t pretend to have all the answers, but there are useful guides to follow. In the words of Spartacus “War has always been a convenient human-shredder for the overclass. It has always been this way. …It’s a scam. It has always been a scam.”. We’re reminded to consider who has always had a hand in orchestrating and profiting off wars: the powerful. Unfortunately, this isn’t immediately helpful. Just as the atom bomb changed the balance of power between nations of the world, network warfare, where dynamic super-national forces engage in a global civil war, the game has changed immensely. As super-wealthy cliques accrue wealth and power that rivals nations, governments themselves can easily become mere strategic objectives in larger games.
It is arguable that network warfare has been the essential root of all human warfare throughout history. The only difference is that both people themselves, and our means of waging war, have the potential to be so disconnected from pre-existing structures of tribes, faiths, or nations. Never before have the warmongers of the past had the entire world potentially at their mercy, as well as the entire population. This form of warfare is total unrestricted warfare, and encompasses all aspects of participation in human society. It has been said that ’the person is political’, paired with the acknowledgement that politics is warfare waged through other means, we understand our predicament more clearly.
There is a way to keep this simple, without losing the important details. People feel under attack, and they are correct to feel this way. This is because unlike what AI evangelists or ‘Net Zero’ malthusians will tell you, human beings are the prize. Not just the prize, but the only prize. Tyrants of all scopes of ambition realize that the source of all earthly power stems from effective cooperation between human beings. This requires them to use more and more sophisticated means of coercion to not undermine the value of total control.
The point of sharing this is that you understand what “side you’re on” is a much more complex question than various accidents of birth. The physical, economic, and even digital empires run by many or even a few are competing for dominance over you and others. Lending your strength or allegiance to one may or may not be mutually exclusive with others. This naturally leads one to wonder if they can opt-out entirely, and abandon the game of conquest and live a life of peace. We can always pray this is possible, but it’s important to recognize that we inherit circumstances that make this require much more intense work than merely not choosing to commit overt aggression.
Conceptualizing a Global Civil War
Economic control is no less devastating than bombs or bullets. Even when direct violence is involved, there are a wide array of ephemeral ‘slow-kill’ means available. Biowarfare, toxins, or even sabotage of essentials are all means to cause mass poverty, suffering and death. Normalcy bias and plausible deniability allow atrocities to take place without recognition or recourse. Quiet weapons doing minor cumulative damage can make a significant impact despite going undetected and being difficult to attribute. To make matters worse, responsibility can be diffused by providing a vast array of self-destructive means of illusory relief.
A Fractal of Suffering
Almost everyone can intuit simple cause and effect, most of the time. What’s much harder for many people to grasp is force multipliers. Various techniques such as propaganda, spycraft, or even financial engineering can make relatively straight-forward attacks work through an incomprehensible maze of complexity. In these circumstances people only identify the pain, not the source of it. This can often lead those who don’t wish to feel guilty to justify the existence of that pain for their own comfort.
Overheated Threat Awareness
With attacks coming from seemingly nowhere and everywhere, there is a natural desire to identify threats. This desire can be leveraged by propagandists and profiteers alike to further their own ends, exhausting the reflex. As people continuously transform themselves into the boy who cried wolf over and over, the populace becomes numb to the sensation of danger. In circumstances where this numbness has taken hold, people are no longer able to act on their self-preservation instincts, creating easy targets for even the most blatant schemes.
Propaganda
The “information landscape”, which is an abstraction of everyone’s thoughts, perceptions, and available information is a valuable strategic target of tyrants. The ability to control, restrict or modify the flow of information gives anyone a significant advantage over others. Pairing this with sophisticated understanding of people’s natural desires, fears, and hopes is a phenomenally powerful weapon to wield against individuals and groups alike. Beyond merely being a blunt instrument to rally compliance, propaganda can be weaponized to turn people against themselves, even individually. This immensely toxic pattern mass-produces hurt people who are readily able to hurt others.
Merchants of Death
War can be big business for propagandists, profiteers, and plunderers alike. It provides the state the pretext to more overtly and more aggressively dominate the financial system. This leads to the mass financial and social engineering of the economic structure to support the war effort.
To illustrate how U.S. military and intelligence agencies have supported tech startups, consider the case of Keyhole, a small San Francisco-based company that developed software for creating three-dimensional models of the earth’s surface. By patching together satellite images and aerial photos, the program could essentially produce a high-resolution map of the entire planet.
In-Q-Tel provided seed funding in 2003, and within two weeks, military and intelligence agencies were reportedly using Keyhole’s software to support the U.S. war in Iraq. The following year, Google acquired Keyhole for an undisclosed sum. It was renamed Google Earth and today, it is worth approximately $4 billion. In this case, In-Q-Tel’s investment paid off in monetary terms, but the bigger jackpot was the Keyhole program itself, which the CIA and Pentagon immediately deployed in support of military operations.
Like many DIU and In-Q-Tel investments, Keyhole-Google Earth is a dual-use technology that can be adapted for both military and civilian applications. The vast majority of In-Q-Tel funded startups acquired by large tech companies have created dual-use products, such as AppThwack and Elemental Technologies (acquired by Amazon); Acompli and Perceptive Pixel (acquired by Microsoft); Tacit Software (acquired by Oracle); Cleversafe (acquired by IBM); MindMeld (acquired by Cisco); QD Vision (acquired by Samsung); and Pixim (acquired by Sony).
How Big Tech and Silicon Valley are Transforming the Military-Industrial Complex
It’s hard to imagine the long-term incentive changes when an entire industry becomes a creature of the MIC. When states and super-national entities harness such massive economic power to run sprawling computing power to mechanize warfare, is there even possibly room for accountability? How does all this spending impact journalism, academia, or even governance?
Cyberwar
When people imagine cyberwars, they often think of shocking news stories of ransomware attacks by shady hacker groups. This is a very serious concern, but another quite troubling development is the digitization of warfare that has accelerated since people’s very lives have become technologically transformed.
The technological dimension of warfare is staggering. There was a time where the most horrifying technological terror was the atomic bomb. While not eclipsing its destructive power, various tools of precision like drones, surveillance infrastructure, or autonomous weapons can be part of the construction of all manner of inhumane horrors. The tragic irony is that warfare has generally been quite human. Warriors throughout history taking up arms against other people across the globe, or even withing their own regions, have always had to contend with the atrocities up close. It seems that we may be on the cusp of witnessing this change in real-time.
Surveillance
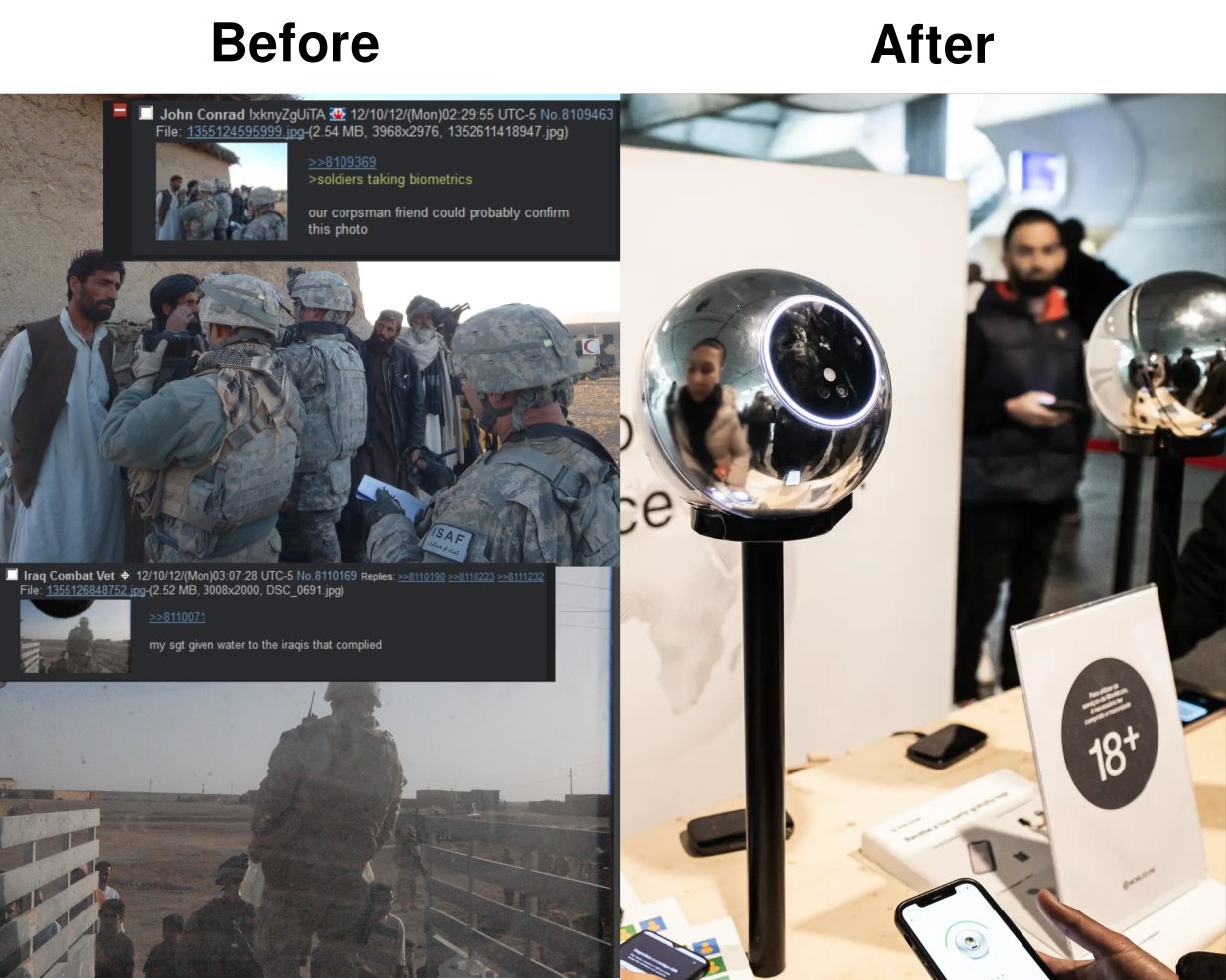
Data collected for seemingly innocuous purposes can quickly become military intelligence. There are many non-intuitive uses for even seemingly insignificant data-points collected over time.
Using AI from Palantir, an American firm, Ukrainian counter-intelligence fishes for illuminating linkages in disparate pools of data. Imagine, for instance, an indebted divorcee at risk of losing his flat and custody of his children who opens a foreign bank account and has been detected with his phone near a site that was later struck by missiles. In addition to such dot-connecting, the AI performs “social-network analysis”. If, say, the hypothetical divorcee has strong personal ties to Russia and has begun to take calls from someone whose phone use suggests a higher social status, then AI may increase his risk score.
A serious challenge caused by industrialized surveillance is information asymmetry, where information is known to few but unknown to great many. The first casualty of war is the truth, and this is never more clear when immense amounts of data are collected in secret to be used selectively. Just as cyber threats blur the lines between military and civilian targets, domestic surveillance becomes more of a priority for troubled regimes.
Machine Learning
It would be naive, if not outright dangerous to underestimate the consequences of military use of machine learning, and how it can move to dominate our lives. Artificial intelligence is its own buzzword, but one must not fall into the trap of thinking it’s all worthless. The more a problem (or killing) can be accurately reduced to a simple set of variables, the more effective these tools can become. Another danger is that many downsides of contemporary AI tools are still serious concerns. Machine errors can be devastating and must not be used to downplay accountability.
The military industrial complex (MIC) is a terrifying machine. Media, industry, and economy are all impacted directly or indirectly by it. Between 2022 and 2023 US Department of Defense spending on AI related contracts jumped from $269 million to $4.3 billion. It is concerning at minimum that this huge amount of resources in military uses of machine learning effectively drains talent from non-combat uses, which could actually improve people’s lives and solve serious problems. While it is true that military advancements in technology eventually trickle down this only happens after an immense amount of avoidable suffering, it is not without cost either.
Dominating Cyberspace
The Internet, despite it’s flaws, is a valuable tool for transmitting critical information. During times of conflict it is a common tactic for powers to cut off access as a means of restricting information or aid. It is a mistake to believe that an Internet shutdown means that others can not use their own private (or military) networks to maintain connectivity. This means that Internet shutdowns are a measure that overwhelmingly impacts civilians and may have much smaller cost for the initiator than one would assume.
Cutting off internet access can also be done in parts. Sophisticated techniques can be used to deny, filter and even manipulate content given enough resources. In many circumstances, it may be preferable to simply inspect network traffic rather than outright block it. Interfering with communications changes behavior, but silently monitoring generally doesn’t.
Cyber Attacks
Just as the lines between the physical and digital realities blur in our lives, so too do they in warfare. The more critical systems that depend on inter-connected online services, the more brittle and vulnerable people are to malicious (state-backed or not) entities. The impact can be devastating with little distinction between civilian and military targets. Because of this, major cyber attacks certainly get the headlines. The impact of disruptive attacks on infrastructure can not be over-stated, but the risk management solutions by the regime can be just as troubling.
Governments have made it clear that information counter to their interests being disseminated itself is seen no different as a ‘cyber attack’. In recent years there has been greater emphasis on manipulating minds in the name of safety and national security. This is a troubling new direction in justifying the elimination of free expression, and justifying propaganda operations. A regime that treats it’s own citizens as if they were any other computing resource will justify very troubling means to meet its objectives.
As non-combatants, it is not merely enough to demand secure systems. It is crucial that we do not allow the fear of cyberwars to allow institutions to take over our digital or actual lives. There is an immense pressure building for people to set aside digital autonomy or even their civil rights in the name of safety. One must be cautioned that conceding these is a road to supporting atrocities without even the pretext of accountability. By being cow-towed into dependence on the regime, the public can very well make themselves unknowing accomplices in what they would otherwise resist with all their might.
Mechanized Murder
As mechanized murder has become more advanced, and various technologies specialize into broader “soft-kill” capabilities, the circumstances become grim in unimaginable ways. Despite conflicts feeling vastly distant for many North Americans, warfare is as real as it as even been. For decades we have seen how many techniques and weapons of war are first tested in remote conflicts then eventually assimilated into the domestic control structure.
This raises the stakes when it comes to our moral culpability in supporting such actions. Just as more powerful weapons expand our capacity to unleash terrible atrocities, automated weapons make each decision carry an immense amount of moral weight. Instead of responsibility being diffused between dozens of people, each reacting in the moment, a single person shoulders the entire responsibility for an orchestra of death and destruction.
The technology on offer may fall far short of Terminator-style robots: in Ukraine, the call to engage with a given target still lies with a human decision maker. But for how long?
…
“If you think of AI as drones autonomously and independently making some decisions to strike or not to strike something, there is no such thing yet,” said Fedorov. “But I think that there is a certain future for it.”
‘Our Oppenheimer moment’ — In Ukraine, the robot wars have already begun
Becoming a Peacemaker
If you are not already convinced, I would hope that you would consider taking on the role of peacemaker. The powers that are in play are capable of irreversible damage, not only that but our responsibility has never been greater. Despite what the overwhelming propaganda would have you believe, we all have an opportunity to push for peace. By connecting with those around you and working to understand and resolve even minor disputes, greater impacts can build over time. Bring peace to first yourself, then those around you, so that you can all work against cruelty in all its many forms.
It is good to be proactive in asking ourselves if our words, and actions dehumanize others or build trust and empathy. Taking action in your own life to withdraw your support and presence from institutions and structures that support senseless violence is highly admirable. It is your burden to take on the massive undertaking of consciously evaluating how you support, or hold accountable various human endeavors without losing faith.
When one sees how bleak things are, it becomes easy to judge. We are all born into cycles that must be broken. Feeling superior to others, or more morally righteous is a prideful pathway to turning into what one wishes to fight. Genuine compassion, patience, and mercy are non-negotiable attributes when it comes to building lasting peace. It is painful to witness further pain caused by ignorance or arrogance, but it is typical that people know not what they do. Taking the time to understand other’s frame of mind and how to build trust and understanding is the only reliable path to making progress in dark times.
Header photo Destroyed Residential Building Under Gray Sky
Sharing is caring!
Please send this post to anyone you think might be interested.
If you haven't already, don't forget to bookmark this site!
You can always subscribe with the RSS feed or get posts sent to your inbox via Substack.