Applied Cyberwar: Hardware Exploits
Just how bad is it?
By Gabriel
Published: Oct 19 2023
Cyberwar
Hardware
Cybersecurity
Surveillance
Government
Security
Internet of Things
Recently a rumor that the tragic Hamas attack was enabled by a potential lack of backdoors accessible by western / 5 Eyes intelligence. Despite this, I wouldn’t recommend rushing to order a Huwawei phone for privacy reasons. If my threat model called for investigating hardware attacks, simply changing providers would be insufficient to keep them at bay. Understanding hardware exploits requires a bit of understanding about how systems run, so let’s take advantage of this teachable moment.
You’re definitely going to want to revisit A Non-Combattant’s Guide to Cyberwar and Escalating Cyberwar: Warlord Technology if you haven’t already. The important take-away is that there are very advanced tools for infiltrating systems using software. In addition to this, when working to combat hardware-based threats, you’re going to need serious regular cyber audits.
It’s All Broken
It can sound very bleak when one understands just how vulnerable digital systems can be. The sad truth is that if somebody is willing to spend significant effort, resources, and time it’s not a matter of if, but rather when they’ll be able to breach your systems. At least for now, it can be a reasonably safe assumption that those who make a reasonable effort to protect themselves can at least secure themselves from un-targeted attacks, and otherwise make themselves a less valuable target.
The challenge is that modern hardware and software is essentially a massive jenga tower of accumulated technical debt. For those who require utmost security and reliability, almost everything available today is absolutely unsuitable for that purpose. Supply chain attacks can be done by compromising either the physical components of the device, or the software built into the tech stack. The tech stack is everything required to run software on your device.
The biggest reason why simply switching hardware providers is not sufficient to mitigate hardware threats; is that someone capable of intercepting a shipment sent to you can then attack the device directly. If you’re already concerned about government surveillance, especially targeted surveillance, you’ll need a proper way to validate that the systems you’re using are free of unwanted changes, bugs, and not tampered with. In addition to this, you’ll want to make sure your verified clean hardware actually Respects your Freedom!
While hardware backdoors are a serious concern, it’s important to pay serious attention to the software environment you’re running. There’s absolutely zero point making changes aimed at mitigating hardware based attacks if you’re planning to run software that is known to spy on you on behalf of the same organizations. With all that out of the way, let’s take the topic head-on.
The Hardware Attacks
If the manufacturer (or manufacturer’s suppliers) introduce a defect or modification to their product, that modification can be exploited. Naturally the defect would be exploited by those who put it in there, but it’s worth understanding that the very same defect could be exploited by others. This is why it is of utmost importance that we the public make it exceptionally clear that we will never accept undermining security or privacy in the name of safety, especially when it empowers unaccountable entities. In the long-run the only solution to this problem is designing hardware so that it can be independently verified with only a moderate amount of effort and tools.
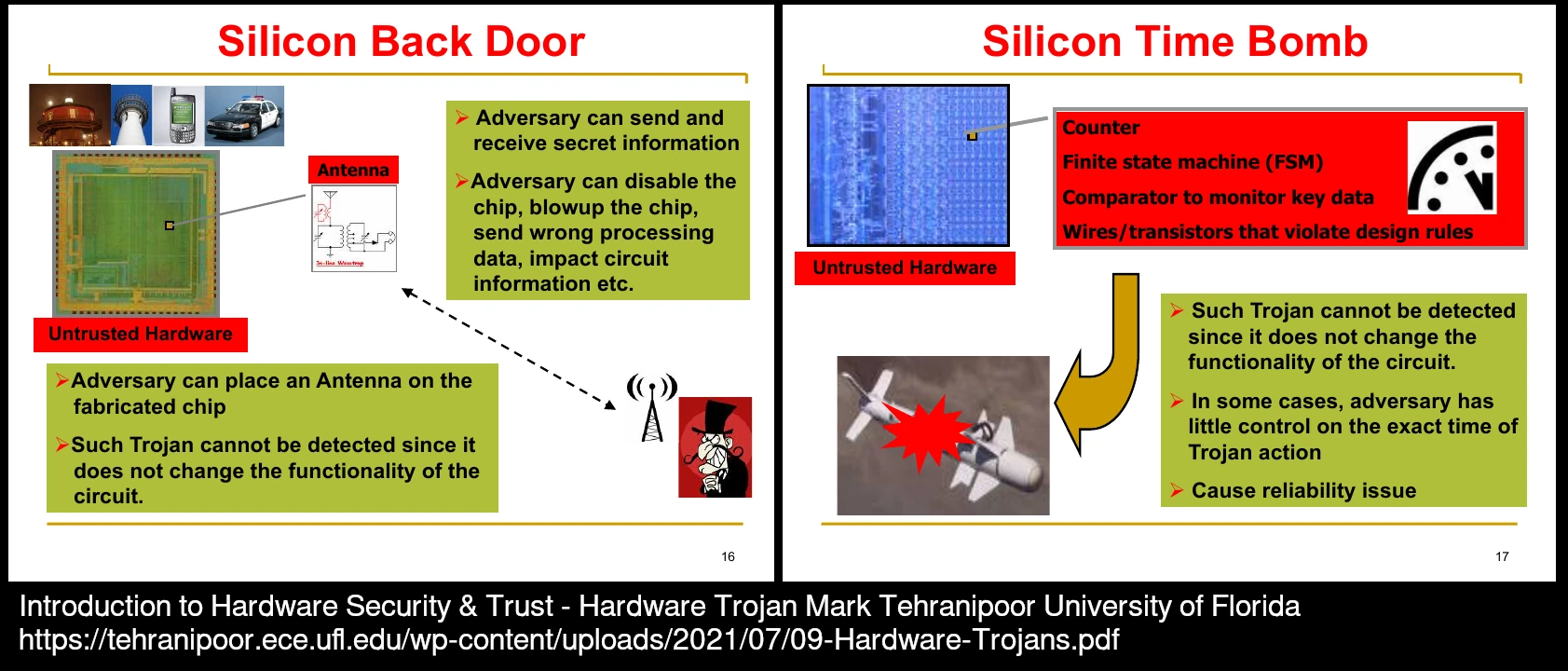
Almost every device is complex enough that it’s not all developed by a single entity. A single company could place a nefarious component into their portion of a device. It is safe to assume that most manufacturers would be testing for defects to detect obvious intrusions, but what if the modification doesn’t impact device functionality? There is currently a lot of research into this. I’ve come across a couple of papers discussing fascinating strategies for detecting that.
Antennas are strange devices, the little I’ve spent learning about radio communications has made me realize how little I understand about these devices. In a really strange way, anything can be an antenna if it’s run with enough power, at a high enough frequency… Wireless communication definitely is one of the more interesting developments. To say nothing of some of the more bizarre advancements like quantum computing.
Even as a highly technical person, it gets really easy for the layers of abstraction to fool you into assuming that lower level details like hardware and firmware are always pristine. It’s important to understand that at a fundamental level all these devices do is store, process and relay information. It’s quite possible for a device to use information sent to it in deceptive ways, and there are very un-intuitive attacks at the physical levels. These threats are very serious and almost impossible for a single person to attempt to mitigate. If it is the case that all our institutions are hostile, corrupt, and incapable of reform, it is then long past time for people to proactively cooperate on establishing the means to design, manufacture, and validate devices independently.
Firmware
Alright, so you’ve used the latest and greatest techniques to validate that your hardware is free of any hardware intrusions or defects. Your team has triple-checked the specifications of every component to the smallest detail, and tested each component for common problems. As you start running software on it, you start to detect strange behavior. Suddenly, your device that you spend so much effort validating isn’t working as intended.
You re-compile all your software from scratch in an effort to solve the problem, but it hits you. There’s a whole layer of code between the software and the hardware. Many hardware components are themselves programmable. A passive component is something that serves a very simple and direct purpose, like a light that shines with power. Logic circuits are components that themselves have memory that allows them to be programmed with additional instructions or parameters that defines how they process information.
It may be complete overkill for a rogue intelligence outfit to compromise an entire system. Instead, it would be much easier to introduce changes to the closed-source firmware on the wireless radios for all kinds of smart devices. With that level of intrusion, it would be very difficult and expensive for someone to detect and correct, and the hardware and software would be none the wiser. This is why it’s important to not only insist on free as in freedom software, but hardware and firmware as well.
Some other interesting videos:
- Spyware at The Hardware Level - Intel ME & AMD PSP
- How Intel wants to backdoor every computer in the world | Intel Management Engine explained
- Dissecting the AMD Platform Security Processor
- GOD MODE UNLOCKED - Hardware Backdoors in x86 CPUs
Machines Can Lie
Programmable chips are incredible tools. So many amazing possibilities are enabled by the fact that they often are designed for abstraction. For example, a display may not actually expose direct control over all it’s nitty-gritty details, but instead accepts commands to display pictures and text. This can make it much easier to build a simple device, but it comes at the cost that the other components sending the information are unable to ensure that what was sent is actually what is displayed. With this understanding, it’s quite easy to see why security is such a hard problem. On some level, it is all downstream of physics.
It is clear that governments, corporations, and intelligence outfits have the means and motive to corrupt our devices and systems. We are aware that this happens in a non-zero amount of cases, including in western countries. It is anyone’s guess how deep and how pervasive the problem is. It is an important problem to keep in mind when thinking of what direction we want our tools to go in, and how we intend to use them. On the other hand, I find this information not to be terribly practical on a day-to-day level. A big part of this is the fact that it’s often very unnecessary to compromise hardware to spy on people or steal their data. If anything, people themselves have shown themselves to be all too willing to comply with surveillance and control if it’s merely sold under the right pretext.
Personally, I believe the best way to act on this knowledge is to realize the dire necessity of building genuinely transparent, efficient and accountable institutions that can work to tackle these difficult problems. We can’t do it alone, but I’m more than confident we can get intelligent people together to make some serious progress.
Sharing is caring!
Please send this post to anyone you think might be interested.
If you haven't already, don't forget to bookmark this site!
You can always subscribe with the RSS feed or get posts sent to your inbox via Substack.