Tools of the Technocracy: #4 Online Identity
What is following you in your digital tracks?
By Gabriel
Published: Mar 22 2022
Tools of the Technocracy Series
Technocracy
Social Media
Accounts
Privacy
Digital ID
Big Data
Voiceover
Tools of the Technocracy: #4 Online Identity
There are some good reasons to attach your identity to online interactions, there are just as many (if not more) good reasons not to. It is important to understand how your actions ripple across the Internet and wider data-landscape. One of the greatest challenges in keeping your data secure is the fact that the Internet almost never forgets. It’s so difficult to be aware of all the data-points that have built over time.
Even if you are a very open and public person, it is vital that you are in control of what data about you is collected, stored, and analyzed. Instead of having systems actively probing you for any and all data they can seize, it is better to understand and use systems that give you the control to only disclose what you want to share.
Concerns
Conformity
Social media has been largely what closes the loop between you staring into the data abyss, and the data staring back at you. By learning peoples’ interests, likes and dislikes the algorithms are able to put that information to use to manipulate them. The most dangerous part about social media is the capability to leverage your self-image against you. With even relatively simple techniques (such as suppressing the visibility of a particular post) these systems can manipulate how your social circle reacts to specific information.
Facebook is really old news when it comes to data-mining people. Tiktok is the state-of-the art, in learning from people. Tiktok has advantages that older social media platforms don’t. It’s purely mobile focused, which means the app has access to all kinds of data from your mobile phone. This includes cameras, microphones, location data, and even how you’re holding the device while scrolling. It would be foolish to assume we can imagine all the ways advanced algorithms can be used to study and manipulate people. How many people would even consider facebook was up to this in 2011-2013?
Echo chambers
This conformity, is the foundation for a fractal of echo-chambers, all becoming isolated from the larger whole. Echo-chambers create divisions within society that eventually make cross-communication almost impossible. By entrenching people into their sub-groups and turning them against each other, everyone is effectively silenced. This is an under-estimated effect of chilling effects.
I believe it is naive to operate under the assumption that these echo-chambers are a purely organic phenomenon. Manipulating the human mind is a massive, and well funded academic venture. The power gained from destroying people’s ability to collectively search for the truth is immense.
If covert censorship wasn’t bad enough, there is a vast array of censorship and suppression tools available. The more information the system has about you the more it has at it’s disposal to use against you and ideals you may support. The ever-increasing cries of “fighting misinformation” and “combating hate” are used as a pretext to justify further centralized information control.
Personification
Now back at you, all these tools are specifically aimed at identifying, storing, and analyzing your every action in the hopes to get leverage over you and others. Very subtle and innocuous information can be correlated with other data to make unthinkable associations.
They will shut it (Bitcoin) down not by controlling the technology, but by controlling the people.
Catherine Austin Fitts
You can leave behind a banned account, even evade region locks with a VPN, but it’s not easy to get a new identity and almost impossible to erase your online footprint. The more online systems demand people turn over their identities online, the more people are vulnerable to all kinds of threats. Dissidents can be marked for life with no recourse. Naturally these people will be restricted from the digital financial complex.
Stalking
Not only are exposed people vulnerable to retaliation from the state, but in an increasingly polarized environment people will be vulnerable to retaliation from anyone who has access to their information. As the dehumanization of the opposition continues, people won’t draw the line at harming innocents if they are led to believe the situation is dire enough. No transgression will be too small to justify retaliation. How many times have we seen people respond to someone losing their job over past comments with “Freedom of speech isn’t freedom from consequences”?
This is a clarion call for abusers and petty tyrants. The very reason the rule of law and the presumption of innocence are important is because the spillover damage from vigilante justice is unending. In our modern enlightened age we certainly have managed to forget basic problems that have been with us since the dawn of civilization.
Children
As someone who spent time exploring the Internet from a young age, I can certainly admit to being unable to comprehend the dangers at the time. As grown-ups today believe that their parents were clueless about technology, the exponential growth, escalation, and evolution of online threats have left current and future parents woefully outmatched. Children won’t simply be at the mercy of their own potential actions, but the actions of relatives and even friends.
As a parent it is your responsibility to make sure that they are prepared to face these dangers, but also that your information is not making that more difficult. Safeguarding them from all the new and tantalizing services is going to be a very difficult challenge. This is an area that needs more research.
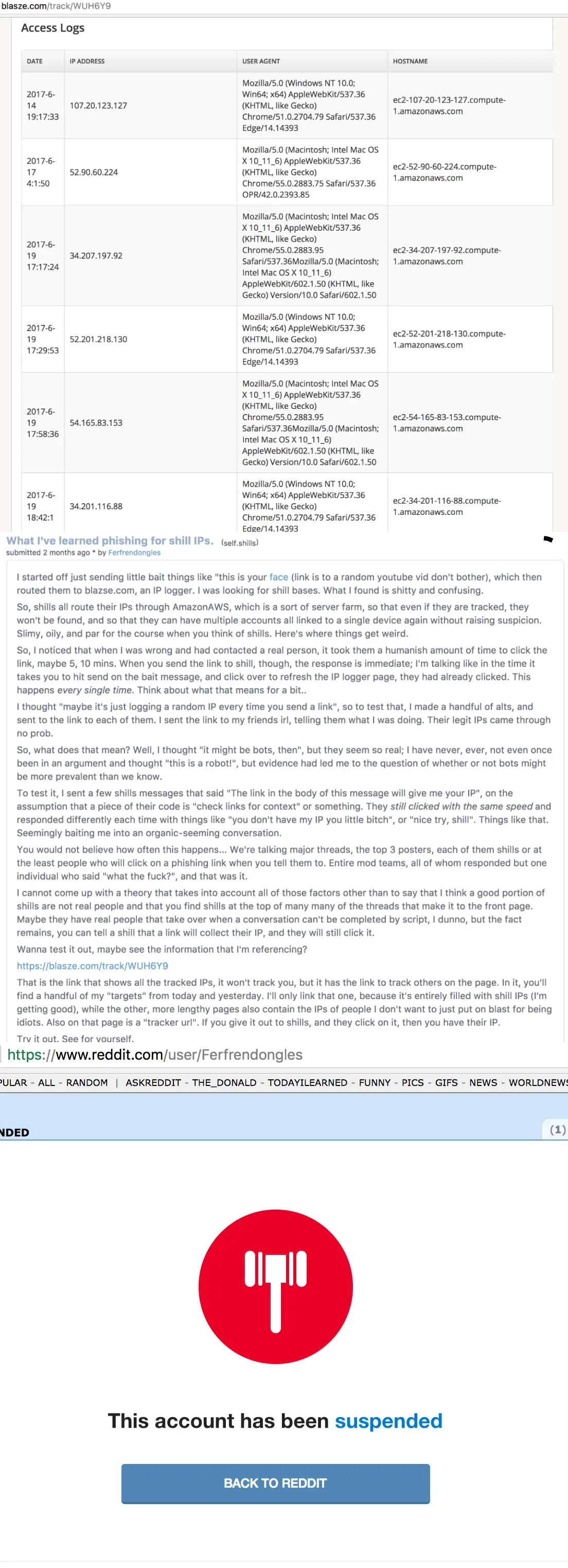
Bots & manipulation
Humans are outnumbered! In many circumstances there is little reason to believe that the person you are talking to online is even human. This is an incredible problem when empathy is already severely lacking in online discourse. As bots get better and better at convincingly imitating people, people will feel more and more overwhelmed which will contribute to some simply choosing not to bother speaking at all.
Botting social networks isn’t necessarily a zero-sum game. Some platforms are easier for smaller actors to influence, it is a critical mistake to assume all bots are from a single interested party rather than a group of varying (sometimes overlapping or conflicting) agendas.
Anti-anonymitity
Anonymity gets a bad wrap in online discussions. Far too many people consider it “cowardice” to speak out without having your name, reputation, and future at stake. This is not a compassionate or reasonable stance to have in an age with so many asymmetric power imbalances. It is a very convenient way for those perfectly within established orthodoxy to throw stones from their glass towers. The most vital way to undermine centralized information control is to prevent knowledge from being judged by it’s origin. A fantastic way to achieve this is publishing information, data or communications anonymously.
Your online tracks
Personal devices
Every device you come into contact with has the capability to be turned against you. Smartphones are some of the worst. Devices with microphones can record your every word and expression. Cameras can track your expression. Worst of all is location data, which gets more and more precise as technology improves. All this is simply assuming the device is working as intended, phishing attacks can be used to gain even more intimate access to your information or otherwise do you harm.
Big Tech Social Media
Many people complain of social media “holding their real-life contacts hostage”. It is very important that you aren’t gating social interaction with you behind data-mining social services. This does require a fair bit of effort and a willingness to compromise. Social media becoming the “town square” wasn’t an inevitable development, it was a necessary step in the encroachment of digital systems dominating our entire lives. You may have a right to remain silent under your laws, but unfortunately your data doesn’t make use of it.
The technocracy’s vision of what social media is and should be is evil. Until we can migrate people to services that put people in charge of their data, it is best to avoid putting any significant importance on social media under the control of corporations & government influence.
Online services
There is no way of knowing for sure an online service you use isn’t simply sharing data with big tech in the first place. Even if they adamantly refuse to share or sell data that all evaporates when the company is sold. Services can be hacked and the only way to protect sensitive data is to never record or share it. Understand that everything you share with any particular online service can eventually be used against you.
Digital ID
Digital ID is the crown jewel of technocratic totalitarianism. Like any other deal-with-the-devil scenario it will be attached to many luxuries and conveniences… at least at the start. Take any of the problems in this article and make them 10x worse. There will never be any guarantee that digital ID systems will be any more secure than systems that came before it. The terms of the digital ID program may appear to be favorable at the beginning, but once locked in… the terms will be altered and your only recourse will be to pray the terms aren’t altered further.
It is impossible to overstate the importance of preventing, resisting, and outlawing the implementation of digital identification. Merely avoiding it yourself will be no protection, as those entrapped in the system will be weaponized against you. The weaponization of people who have fallen prey to centralized information control is a mere taste of what is to come when people are locked into a digital gulag.
Solutions
Connect with people in real life
Be the person to provide the authentic, uncensored human experience with those you care about. The fight to maintain human liberty is bigger than any one of us. Bring joy outside of online experiences and focus on the people around you.
Provide people with a more secure form of communication
By having multiple good options for people to try you don’t have to try to force everyone onto a single app/system. Some great options are:
- Delta Chat
- Session
- Element
- Signal
Improve your account data and security.
Federated social media
Self-hosting
Want to be entirely on your own terms? Running your own website is a way to have complete control while still being able to maintain a presence. These two sites have great guides for getting started.
Sharing is caring!
Please send this post to anyone you think might be interested.
If you haven't already, don't forget to bookmark this site!
You can always subscribe with the RSS feed or get posts sent to your inbox via Substack.