Why The Perfect Messaging App Doesn't Exist
Making sense of security limitations
By Gabriel
Published: Dec 10 2023
Privacy
Social Media
Surveillance
Encryption
Censorship Resistance
Security
Surveillance of peoples communications is a severe overreach. Especially the act of monitoring people’s sensitive discussions with their most trusted contacts. Large institutions like corporations and governments are wrestling over control of and insight from people’s private chats. This is largely because there are limitations to only data-mining public communications. All the money and effort spent on propaganda and censorship can be for naught if people are still allowed to make their own minds in private. This is why since the Covid Crisis there has been a rise in research into how to limit speech in private communications.
Already, there have been many proposed regulations all over the world, aimed at securing control over people’s ability to communicate. Most infamously, we have the EU’s ChatControl & Digital Services Act. It’s important not to forget that corporations themselves already wield a significant amount of power over public and private communications. While governments helping themselves to slices of that pie is a problem, we should reconsider our role in baking it at all. This is to say, we are all responsible for top-down control of communication with our choices to use platforms that enable it.
The cost of apathy is quite high. If you’ve been at all concerned about the ability for consent to be manufactured across a variety of issues, it will only be exponentially worse when people aren’t permitted to dissent in private, much less public. If that isn’t bad enough, there is a sense of defeatism and helplessness by those who haven’t begun their journey to take control over their computing. Those who don’t truly appreciate the benefits of free software are very prone to seeing it as an all-or-nothing affair, forgetting that incremental change can have massive benefits. Often, critics of more privacy-focused tools will underestimate the problems from more popular systems.
Understandably, you have to take your first steps to truly feel the difference. While I encourage you to learn how to store your own files, host your own services, and use a variety of Free Software tools, this piece is about why there is no silver bullet to online communications. Of course this applies to much more than just instant messaging software, but it can be a useful example to highlight a wide variety of important issues. If we truly want to improve our technological landscape, we need a serious and thoughtful approach to understanding the problems.
Why The Perfect Messenger Doesn’t (Yet!) Exist
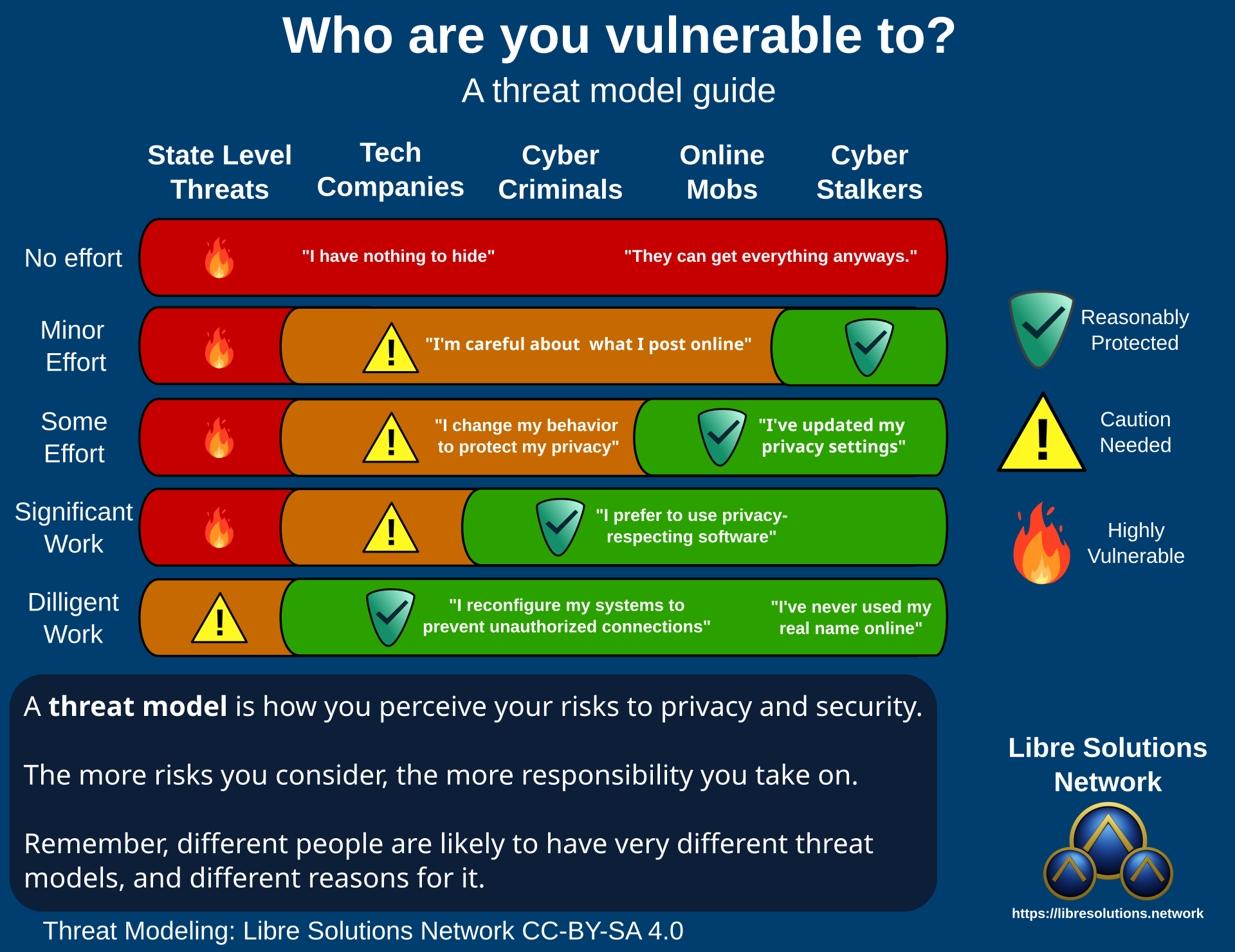
People really need to stop letting the fantasy of perfect security get in the way of making gradual improvements. Letting imperfections get in the way of you stepping away from total corporate control will leave you in a very sorry place. See the following threat modeling infographic. Just because you’re still vulnerable to state-level threats doesn’t mean it’s not worth using a secure password, or proper encryption methods.
What is Perfect Anyways?
For the purposes of this piece, the perfect messaging software has the following non-negotiable attributes:
-
Free Software
Free and Open Source Software has a variety of benefits that are highly valuable to those interested in computing on their own terms. Open Source software doesn’t guarantee security, but potentially has the ability to resolve serious issues quickly, and allows for innovation from broader and more diverse perspectives.
-
Self-Hostable
If you’re locked-in to a single provider, you’re immediately placing them in a position of trust. They may be able to provide better security than you could on your own, but in an ideal world you (or your team/community) would have the option to take on that responsibility.
-
Interoperable
Being able to communicate across instances of the server software. This means that large communities, and single users / peer-to-peer deployments should have the ability to seamlessly communicate with each other.
-
State of the Art Security
The perfect software necessarily has to be secure from at least the majority (but ideally all) known risks. This includes threats of impersonation, censorship, and interception.
-
Significantly Cross-Platform
There is no point developing the perfect software only to run on corporate controlled ecosystems. Requiring Some to use a smartphone or other non-ideal software can be a deal-breaker.
-
Expected Features
The software should support a majority (if not all) of the same features people are used to using, such as video and voice calls, Group chats and calls, multimedia, and all kinds of other nice-to-haves.
Additionally, I’ll also define these nice to haves which matter a great deal to gaining traction:
-
Has a Significant Userbase
While obscure software may be sound, safety in numbers applies in digital contexts too.
-
Independently Funded
Either as charity, or a crowdfund, it would be important that the project’s existence is not beholden to a entity that can be controlled.
-
Accessible
Being easy to use is a pre-requisite to being ideal.
-
Highly Configurable
There may be reasons for people to prefer slight changes to the software’s design. It’s important to put the person in control of their own experience.
Maybe You’ve Heard of Something Like That?
Maybe such software actually does exist… or at least in part…Right? You may even argue some of my criteria aren’t essential at all, and that I’m making perfect the enemy of good. You might actually be right, If you have a suggestion that meets a majority of these criteria, let me know and even if it’s close, I’ll do a full review.
Security is Hard. Really Hard.
The perfectionists often really underestimate what they demand. A straightforward solution to one security problem can sometimes make another one significantly harder. Seemingly simple questions like “Where are the messages stored?” can have profound impact on a variety of security concerns. This doesn’t mean there’s no point using anything at all, but it’s important to understand what benefits you intend to get out of particular options. There can very often be solutions that are well suited to a variety of these problems, and the trade-offs may be worthwhile.
Metadata
Metadata is a serious concern. All kinds of additional information about content like who is talking to who, how often, and when can give spies a significant amount of information. The sum total of who you communicate with may seem like innocuous information, but it’s very valuable to those who aim to control the flow of information. Being able to detect when particular figures gain (or lose) influence over others itself is a significant data-point as well.
Securing metadata is a non-trivial problem to solve, especially if you want to have a variety of community & individually administered services. The advantage of having communications go through a single-point is that erasing metadata is as simple as deleting it (or not preserving it in the first place). This becomes impractical for other reasons though, because if one can be prevented from accessing that single service, its metadata protection is…irrelevant.
Encryption
The other side of the coin of secure messaging is encryption. Your messages need to be safe from prying eyes in transit and at rest. There are many factors to consider when understanding what encryption features are available. When information is encrypted with a key, those who have access to the key(s) will be able restore the original information.
Key Management
When messages are encrypted, whose keys are used?
Are messages secured with the participants keys or is a corporation doing all the encryption?
Where are the keys stored? On the device, or with a service provider?
These questions have profound impact on the security of the system and people’s messages. Simply taking encrypted to mean secure is an easy trap to fall into.
Key Exchange
When someone starts a chat with someone new, how are keys exchanged? Are the keys shared by users directly? Or is a service provider assigning keys to each participant?
End-to-End Encryption
Are messages secured from being snooped on by the service provider? What are the guarantees that nefarious changes can’t be introduced by the big tech corporation managing the keys?
Encryption at Rest
Wherever the messages are stored for safekeeping, the last thing anyone wants is for those messages to be stolen and revealed. This means that the messages need to be stored privately, as well as encrypted in case the storage is compromised.
Perfect Forward Secrecy
It’s a bad idea to have a single key for every message, to protect messages across time they need to be secured with a unique key individually. This means that if a key is discovered or revealed, it can’t be used to decrypt past and future communications.
External Threats
Interception
Even if your communications are secure, it’s possible that they may still be intercepted and stored. This gives attackers time to try breaking encryption as technology advances and more sophisticated techniques are discovered.
Software Environment
Your messaging software may be perfect, but that may not prevent other parts of your system proactively attempting to spy on you. Even something as innocuous as the notifications system on your smart phone can be used to steal information.
Interlude: Why is this Worth Understanding?
It’s critical that we get key management right. After countless data breaches and hacks, it’s understandable that institutions want to move people away from difficult (if not impossible) to secure systems like email and sms. You’ll notice, both of these systems are used for authentication. Not only that, but sms for 2nd-factor authentication is also what has increased people’s dependency on smartphones. We have a chicken and the egg problem when it comes to authentication. Switching to new systems ultimately requires some way to practically solve key management.
Diving into Authentication
There is a great push to end online privacy for all kinds of reasons. Governments and corporations don’t really have incentives to protect you from risk, but rather want to protect themselves from your risk. This is why many workplaces will issue their own devices, locked down under their control and governments are seeking ways to digitize personal identification.
If we truly want to be in control of our own digital identities, and how they can and can’t be used, it’s critical that we refuse to be boxed into identity systems modeled after feudalism. Of course, escaping it by oneself is hardly sufficient, as liberty-minded individuals it is of utmost importance that we empower others to also refuse digital tyranny. Tools are a useful part of this, but so is understanding the proper boundaries.
By allowing a corporation or government to assign you a sole, permanent, digital key management system under their control, you’re not a client but a subject. Suddenly as that authentication mechanism becomes embedded in other areas, such as entertainment, finance, and even social interaction one can be penalized in all kinds of cruel and bizarre ways. While using a single, intuitive, and permanent authentication method for everything may seem convenient, it’s going to have troubling drawbacks if people don’t have at least the option of self-custody.
Hardware authenticators and global password-less logins aren’t inherently evil, but it’s easy to see how they will be used to lure people into digital key management systems that take authentication out of their control. This can get much worse as biometrics are integrated into authentication itself. In that scenario it can be much harder to opt-out.
Anyways, it’s worth thinking about.
Back to messaging software.
Common Pitfalls
Reliance on Smartphones
Mainstream smartphone platforms have constant and pervasive privacy risks, even from the manufacturer’s themselves. This makes reliance on smartphones a net-negative for any secure messaging system. Some messengers exist exclusively as smartphone apps, meaning that those who do not use, or would prefer not to use them are locked out entirely. If nothing else, it’s nice to have access to a keyboard once in a while. Requiring a phone number and/or text message to register is functionally the same as requiring a mobile phone to use the system.
Large Groups
As the number of participants rise, encrypting communications becomes more complex, and less useful as the content becomes all-but public information anyways. In some circumstances, it may be preferable to warn users as groups become too large to keep meaningfully private.
Third-Party Integrations
It can be very simple to rely on external providers for additional features. These additional features can come with significant privacy risks as clients make requests to these additional services. This can also include problems and security threats inherited from software ecosystem choices like particular libraries and APIs.
User Experience Challenges
It can be difficult when a piece of software is superior on a large variety of important criteria, but then fails to be intuitive to use. This can be a significant barrier, and may also include accessibility concerns.
Free of Charge vs Paid Services
Who funds development? Where does the hosting for the service come from? These are critical questions to ask about any project, but it’s especially important when it comes to your private communications. There’s also the question of non-technical uses of funding. Does the app have an army of (potentially paid) online marketers? Is it featured in advertising or paid sponsorships? Are donations/revenue used for efforts that are more about politics than improving services?
Open Protocols
Open, interoperable protocols are exciting. They can help separate specific service providers from being the totality of the system itself. In the long run, hopefully these systems become significantly anti-fragile as they’re adopted further. The main advantage of having an open protocol is that a variety of client software can be used, instead of betting everything on a single application. The point of an open protocol is to define a common standard that different systems can all interact through.
When it comes to choosing between Matrix and XMPP, you may want to consider this outline. That said, open protocols are one of the foundational pieces of building a better technological future.
XMPP
The Extensible Messaging and Presence Protocol has been around since at least 2004. It is a fully decentralized protocol with a variety of clients and servers. Definitely worth considering for fully independent communications infrastructure. XMPP supports multiple end-to-end encryption schemes. Since XMPP is an open protocol, it’s possible to build a server from scratch.
Clients
- For Linux/Windows: Gajim
- MacOS/iOS: Monal
- Android: Conversations
Servers
Matrix
Matrix is an “open network for secure, decentralized communication”. The primary client is Element, which is a polished and intuitive cross-platform application. The matrix foundation has some exciting innovations in the works, including VR experiences!
Clients
Servers
Alternative Messengers
Signal
Signal has recently been under harsh scrutiny after recently asking for donations to run their service and beginning testing on using usernames instead of phone numbers. Despite a solid history the hard requirement of using a phone number has been a significant concern.
For those unable or unwilling to run their own communications infrastructure, Signal is a huge improvement over corporate and mainstream social media messengers and boasts quantum resistance. In fact, many of them are adopting a modified (possibly inferior) version of the signal implementation of end-to-end encryption.
For android, Molly is a fully-free open source alternative client. The majority of issues surrounding Signal are inherent to using a phone with google play services.
Briar
Briar is a fascinating project aimed to allow communication over a variety of networks, including bluetooth. Unfortunately, Briar is limited to running on Android and it would be nice if it supported other platforms. Briar is missing some expected features, but it’s censorship resistance features are very sophisticated.
SimpleX
SimpleX is very much in the same vein as Briar. Looks like an excellent and promising project, but sadly is limited to smartphones. SMP servers can be self-hosted and the documentation is quite good.
Jami
Jami is a peer-to-peer communication suite available for android, Windows & Linux. It can also function as a SIP client to make ordinary phone calls. Jami can take a bit of time to learn, but has a wide array of useful features.
What to Choose?
I generally recommend not putting all your hopes into a single option. By restricting your choices to a single option it can be difficult to coordinate with others. Being flexible can help, but this should be reciprocal. Everyone’s situation and desired results will be different, but in general I recommend using the most secure options that you and your contacts are willing to learn/adopt.
This is no trivial task, which is why you should help inform your contacts why taking their own privacy and security affects them and you. Many hands make light work, and we can achieve a lot when we work together.
Potential Game-Changers
None of this means we are doomed forever. There is a great deal of opportunity in working to resolve these problems. Not only that, but there are some key innovations that would go a long way to tipping the scales in favor of secure self-custody communications.
-
Modularity
So called “freedom tech” needs to embrace the “Unix Philosophy”: Do one thing, and do it well. Far too many projects will try to reinvent everything and predictably fall flat while doing so. For example, when developing software for a particular purpose, consider using an open standard like OpenID connect or IndieAuth to let other software handle authentication. Separating authentication from primary functions can allow for other innovations to improve that aspect of more systems.
-
Hardware Keys
A truly Free (as in Freedom) self-custody system for managing encryption keys could help in many areas. A permission-less system like FIDO2 could go a long way to make secure options much more user-friendly. Allowing for greater convenience and greater autonomy.
-
Network Agnosticism
Assumptions made in the past may not hold for the future of a more surveilled and censored Internet. The ability to seamlessly work with censorship evasion and anonymity technologies like Tor and I2P can go a long way.
-
Generative Tools
If metadata is such a big problem, embedded text-generation machine learning models could send out extra communications at random to unused keys. This could make the complexity of mapping actual communications significantly more expensive at minimal computational cost.
-
Custom Devices
People would do well to take inspiration from Beepy which is a custom device one can use with secure messengers. This straightforward concept of a single-purpose device can greatly reduce people’s dependency on surveillance devices.
Sharing is caring!
Please send this post to anyone you think might be interested.
If you haven't already, don't forget to bookmark this site!
You can always subscribe with the RSS feed or get posts sent to your inbox via Substack.