Directive 4 of the Internet
ICANN and our technological landscape
Guest post by Paul
Published: Apr 27 2026
Most analyses of whatever is currently wrong reveal that before the current thing went wrong, there was something else just before it that was also wrong.
When I have meditated on this and attempted to regress as far as possible without analyzing Layer 1, it becomes clear that a key problem that remains unresolved is the exclusive network that limits us and can be weaponized against all of us.
Internet is a word used to refer to all networks using the Internet Protocol (IP) and under this definition a network is not necessarily connected to other networks.
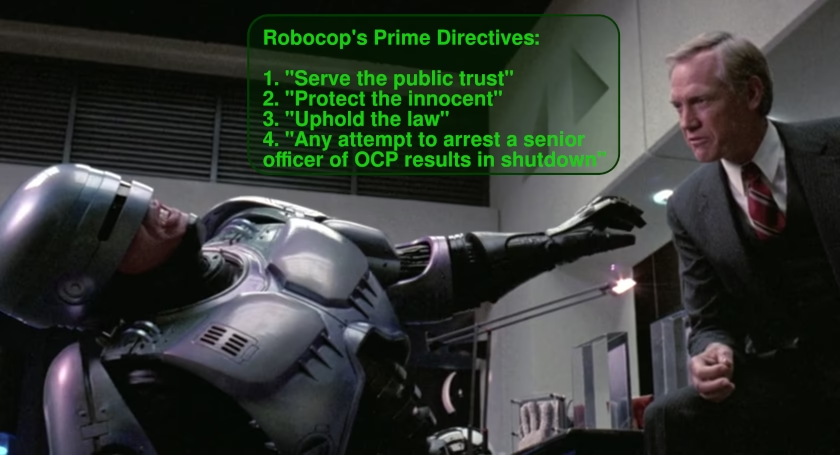
The Internet Corporation for Assigned Names and Numbers (ICANN) controls an exclusive network via their own networking suite. The most critical function of the ICANN-controlled networking suite (ICANN-NS, unless someone suggests something better) is control of addresses and routing. Being that this is an exclusive network, not only can ICANN approve who uses the network, they can expel anyone previously approved.

While ICANN has remained relatively neutral in its stewardship of the ICANN-NS, the suite can, at any time, be weaponized. While most people may initially consider merely the quantity of IP addresses possible and thus conclude that ICANN cannot control every single user, the more useful analysis is on the number of organizations approved to operate within the ICANN-NS – a significantly smaller and more manageable number. Almost all organizations with assigned numbers require having those numbers as a core part of their business. Threatened with expulsion from the ICANN-NS, all of these companies will either comply with whatever ICANN requires or go out business.
It could be said that because ICANN has never weaponized the ICANN-NS against its users, it can also be said that ICANN has not adequately protected its users. In the case of LLM training, it can be argued that more users are harmed by the activities of the LLM bots across the ICANN-NS than benefit from the same bots. The activities of the LLM bots include violating myriad published protocols, notably IP address spoofing. Thus, ICANN is minimally derelict in their oversight and potentially a cruel master.
Networks operating completely independent of the ICANN-NS are sparse.[1] Implementations of mesh networking are usually regional. My personal, limited experience with public mesh networks is that they are heavily saturated and used primarily to access bridges to the ICANN-NS free of charge. I have observed that many people taking part in mesh networking believe that money should not exist and everything should be free.
Another competitive response would be a freely-associative[2] network that includes following protocols to negotiate payment options between nodes and has no central authority.
At the physical layer, real assets are required for any network to function. I believe that my limited experience with mesh networking is at least correlative with fundamentals of economics which would conclude that such a free service cannot sustain itself. Therefore, somehow, physical resources must be available to propagate and sustain a network.
A protocol could be created to quickly negotiate an agreed ledger[3] to be maintained between two nodes. The purpose of the protocol is for node operators to quickly determine if they have compatible payments and to agree on terms for balance settlement.
Since the protocol is very flexible in the sense that it could permit gratis service generally, limited gratis services, physical (or “manual”) remuneration, remote exchange services, or any combination thereof, and to include terms to re-negotiate and scale, node operators would become completely in control of what reaches their nodes.
In the case of LLM bots abusing networks and increasing labor and hardware expenses, the LLM bot operator could be converted into a funder for increased labor and hardware expansion or just go away. Not to mention that the ever-narrowing portal of services available to dissident voices could reverse course, as this could effectively facilitate a universal micropayment system.
This would also have the effect of generally reducing overall hardware requirements at nearly every step, nearly eliminate market viability for DDoS attack mitigation services, and provide marginal ease from the current A.I. industry hardware stack supply chain attacks.
At the same time, it could spark an entrepreneurial boom in the form hyper-local ISPs, such as small roaming nodes, mobile node stations (e.g., parked vehicles, trailers, etc.) and various support services, such as network analytics indicating geographic demand for bandwidth. This would be analogous to dial-up ISPs that formed during the 1990s, which were effectively a precursor to broadband services, establishing a customer base with inexpensive service prior to the more capital-intensive broadband network construction.
The challenge for all such proposed ideas is getting anyone to take any meaningful action. For any action to ever be taken, the idea has to somehow be presented, shared, discussed, critically analyzed, and responded to by both proponents and opponents. Then, ideally, a usable and useful protocol can be proposed, tested, implemented, and maintained.
Notes
[1] The InterPlanetary File System (IPFS) may be able to operate without the ICANN-NS, it is currently not actually useful without the ICANN-NS. If ICANN decided that it does not want IPFS on the ICANN-NS, they could threaten operators with expulsion if they do not exclude the IPFS from traversing their networks.
[2] Not “inclusive,” as this word implies users are required be part of the network and are additionally required to interact with everyone on the network.
[3] The word “ledger” is used in the most generic sense and not to imply blockchain technologies. I would, in fact, argue against blockchains in this application.
Sharing is caring!
Please send this post to anyone you think might be interested.
If you haven't already, don't forget to bookmark this site!
You can always subscribe with the RSS feed or get posts sent to your inbox via Substack.
